- Featured Resources
- Did You Know?
-

Big Games, Big Files, Bigger Challenges
“Now that we have Media Shuttle, we are finally able to replace FTP, which is something our security team has been wanting to do for years.”Read Blazing Griffin Keeps Complex File Movement Simple with Signiant -

DigitalFilm Tree and the Power of Belief
“Signiant, at the end of the day, is helping storytellers wherever storytelling is happening."Read Blazing Griffin Keeps Complex File Movement Simple with Signiant
-





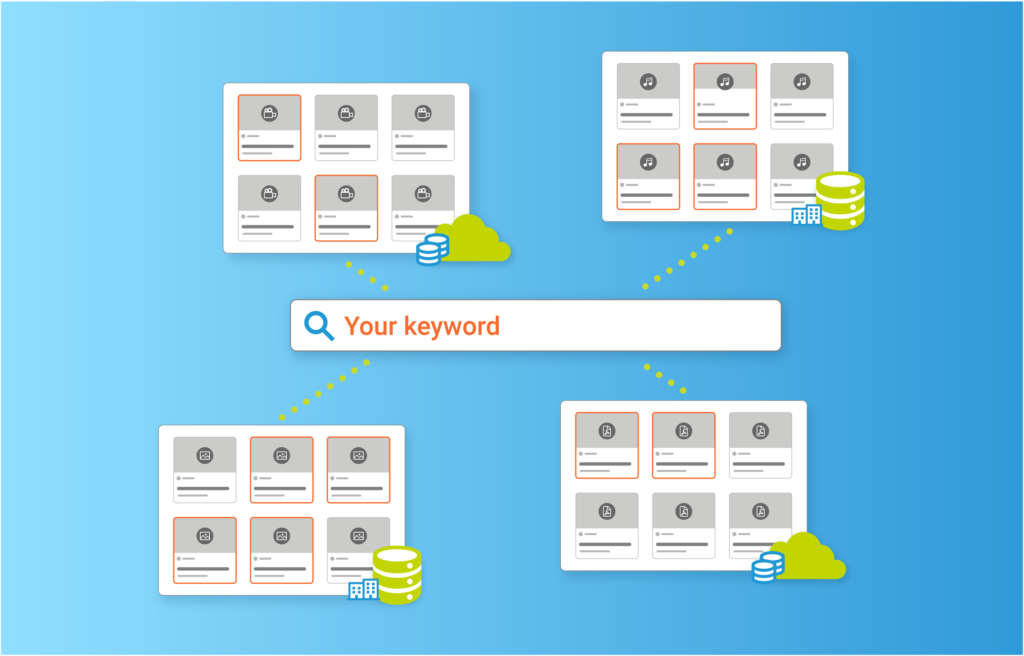
You can search and preview assets across all your Media Shuttle Portals
Already a Media Shuttle customer? You can search and preview assets across all your Media Shuttle portalsRead Blazing Griffin Keeps Complex File Movement Simple with Signiant -





The Signiant Platform can revoke a transfer
Easily revoke a transfer if you inadvertently sent the wrong file or sent it to the wrong person.Read Blazing Griffin Keeps Complex File Movement Simple with Signiant
All Resources
-





Blazing Griffin Keeps Complex File Movement Simple with Signiant
“Media Shuttle came to the rescue. The original camera rushes were uploaded overnight from the location, and we had the footage for our final program first thing the next morning.”Read Blazing Griffin Keeps Complex File Movement Simple with Signiant -


Navigating File Size Limits in the Media & Entertainment Industry
Unlock media industry success with strategies to conquer file size limits and streamline content workflows efficiently.Read Navigating File Size Limits in the Media & Entertainment Industry -


Signiant Secures Remote File Workflows for Mango/NewEdit M&E Productions
“The good news is that because a lot of people in our industry know and use Signiant, it’s very easy for us to set up a vendor with a Media Shuttle account.”Read Signiant Secures Remote File Workflows for Mango/NewEdit M&E Productions -

Big Games, Big Files, Bigger Challenges
“Now that we have Media Shuttle, we are finally able to replace FTP, which is something our security team has been wanting to do for years.”Read Big Games, Big Files, Bigger Challenges -


Blue Ant Media: Staying (Storage) Independent with the Signiant Platform
“We used to run FTP internally. It was a nightmare. We always had problems hosting it. It wasn’t secure at all.”Read Blue Ant Media: Staying (Storage) Independent with the Signiant Platform -

Media Engine Webinar
Looking to discover new ways to manage and access your valuable media assets? Watch this prerecorded webinar and learn how the Signiant Media Engine can help!Read Media Engine Webinar -

The Signiant Platform offers pre-transfer file validation
Have you ever received a file in the wrong format? The Signiant Platform alleviates this problem with CloudSpeX. CloudSpeX checks the file against a selected specification before a transfer and alerts the user if the file is out of compliance.Read The Signiant Platform offers pre-transfer file validation -

Signiant Ices RÚV Iceland’s File Transfer Pain
“It truly simplifies a lot of our day-to-day work. It has streamlined every transfer and everything compared to FTP.”Read Signiant Ices RÚV Iceland’s File Transfer Pain -


DigitalFilm Tree and the Power of Belief
“Signiant, at the end of the day, is helping storytellers wherever storytelling is happening.”Read DigitalFilm Tree and the Power of Belief -


DigitalFilm Tree
“Media Shuttle, for us, is incredibly ubiquitous. It’s in everything, like water.”Read DigitalFilm Tree -


The Bunim Murray Challenge
“We live in that immediacy. We’ve come to rely on Media Shuttle to be our everyday solution and never have to worry.”Read The Bunim Murray Challenge -


The Signiant Platform
What if you could accelerate the way you produce and supply content, no matter who creates it or in which formats, or where it needs to go?Read The Signiant Platform