M&E File Security is a Team Sport
Think of your M&E business as a team sport. Files are the ball. Your creators are your offense, whether they are in-house, remotely located and/or contractors. They score points (generate revenue) by creating amazing file-based content that meets razor-sharp deadlines. Your file security measures are your defense, typically run by your operations and IT people. If your defense is not good, points will be scored against you and can cause your team great pain (loss of revenue or worse).
Your best players on offense don’t always possess particularly good defensive skills. That’s not what makes them great. Media production realities frequently clash with security necessities and there’s still wariness in IT-led solutions. Security teams, particularly in large organizations, need to understand how their creative counterparts do their jobs and what it is they are trying to achieve. Creative people are much more aware of the risks and the range of risks today, but in the production domain, getting the creative done sometimes causes security corners to be cut. So what do you do?
You Need A Game Plan
In order to win, your team needs a game plan that emphasizes production efficiency and tight security. Keep in mind that not only are organizations different from each other, individual projects are full of nuance and different from the next. Each project needs to have its own security game plan. Your game plan must find the sweet spot between ease of use and providing the security you require. If security measures become too much of a roadblock for people trying to get a production done, then your offense will find workarounds. Creatives under pressure might say, “I’ll do whatever I need to do. Don’t burden me with extra steps that prevent me from getting my job done.” This can lead to costly lapses in defense. With more and more work being done through the cloud, the more you’ll have to game plan in order to stay safe.
Essentials for Game Planning File Security
The way forward may not always be clear, but emphasizing planning, education, training and adopting the right solutions with a comprehensive and communicative attitude is the best path toward enjoying the benefits of both optimized efficiency and robust security. There needs to be far better communication between the security specialists and those who are actually carrying out the project and understanding the tools that work for both.
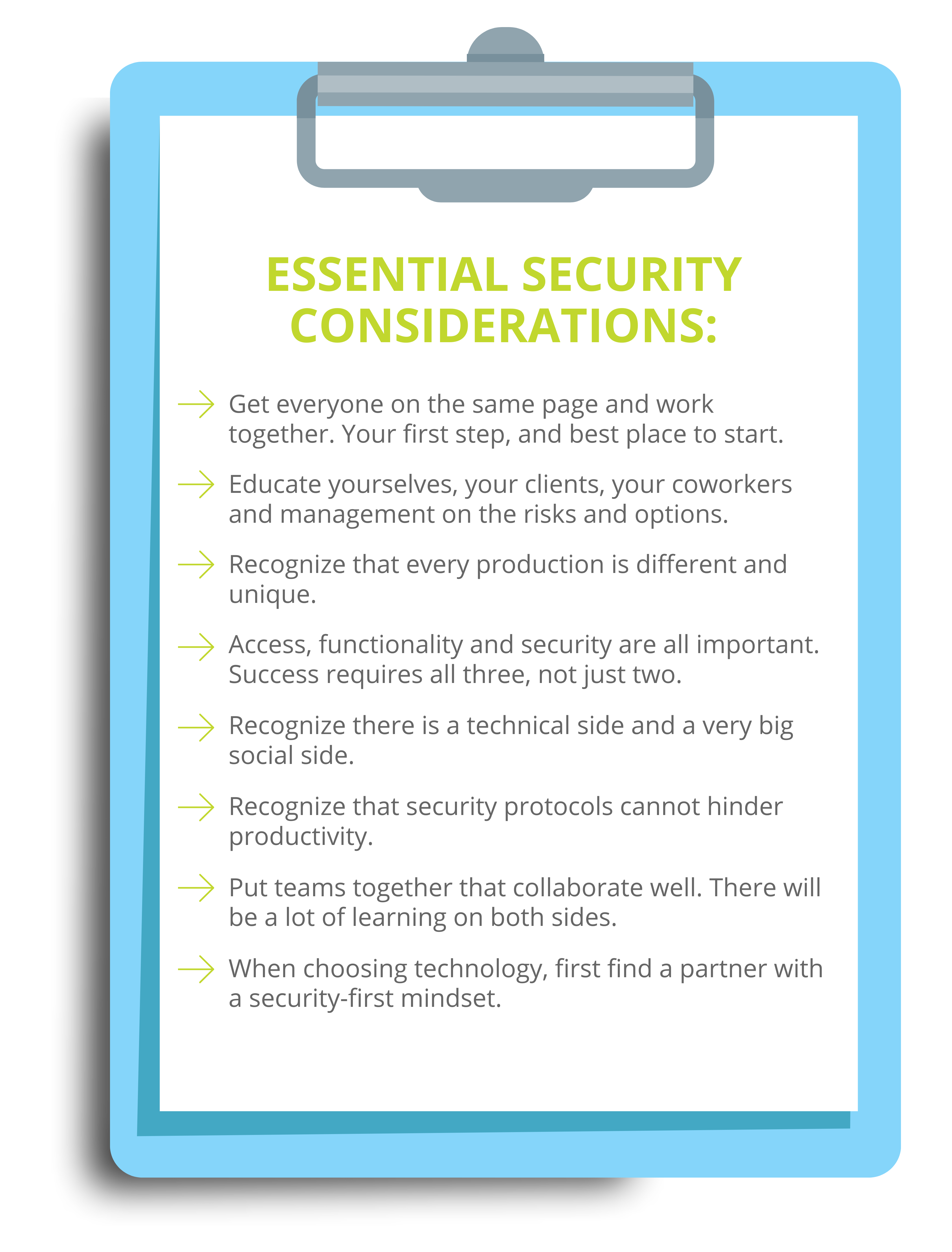
Here’s a brief outline of essential security considerations:
Educating your team on offense is the best defense and puts you in a safer place. Changing your culture around production efficiency and security may necessitate changing how your people operate. Upper management support is vital, but training is just as vital. Make sure that your clients as well as all of your technicians, editors and managers are all on the same page and on the same team.
Balancing and supporting both security and production efficiencies will ensure you are putting a winning team on the field.
![]()