Securing SaaS, Part 1: The architecture of secure design
By Ian Hamilton
File Sharing Solution and SaaS Security
When you’re in the midst of a tedious editorial process, the security of files as they volley among team members isn’t something most people want to think about. Signiant designed Media Shuttle as a hybrid SaaS file sharing solution that is especially conducive to the flow of media production and post-production, but with a backend that appeases IT’s legitimate security concerns about most SaaS.
Leaders in Media & Entertainment and a growing array of other data intensive industries depend on Signiant to move petabytes of high-value digital content every day. Our customers trust us with their intellectual property, delivery timelines, and ultimately their reputation. Effective security is complicated, however — it must encompass all aspects of product development and daily operations, and requires thoughtful application of both policy and technology.
In this four-part blog series, we’ll discuss how Signiant ensures security while still offering the many benefits of SaaS. Part 1 covers the architecture of securing files in transport and storage.
Media Shuttle’s Advanced File Sharing Architecture
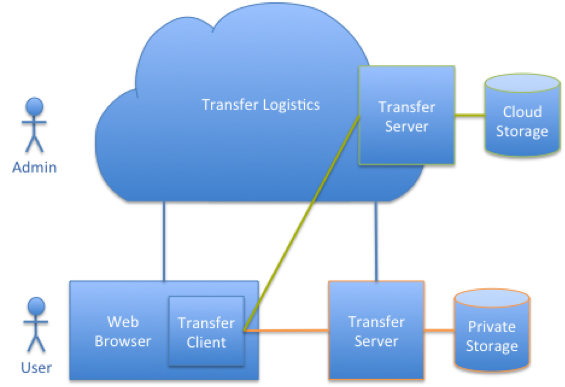
Media Shuttle’s security architecture incorporates a file transfer tier, made up of file transfer clients and servers, and a transfer logistics tier hosted in the cloud. Media Shuttle’s hybrid SaaS technology is unique in offering you a choice between storing your files on-premise or in the cloud, while the software that actually moves files is a true cloud-managed SaaS offering. This eliminates the security risk of most file transfer services — your files are never stored in the same file system or cloud storage tenancy as other people’s files. The advantages of segregated storage are numerous, but from a security perspective it provides an extra layer of containerization.
To break it down a bit: the cloud tier of Media Shuttle delivers the browser-based user interface and provides file transfer logistics support. The cloud tier interacts with transfer clients and servers to move files between user storage and transfer server storage. A transfer client runs as a native browser plug-in for user-initiated transfers.
The following diagram illustrates these components and how they interact:
Fig. 1: Media Shuttle Components
Secure Web Communications
All web interactions utilize standard Transport Layer Security (TLS) to authenticate the server and encrypt information exchanged between the browser and the server. Users log in to the Media Shuttle web interface using their username and password. Strong password policies are enforced and users can optionally authenticate using SAML-based Web Single Sign-On (SSO) with usernames and passwords managed in enterprise and cloud directories.
Web SSO also enables alternate authentication schemes, like multi-factor authentication, and enables enterprise specific password policies. When web SSO is used, user passwords are never exposed to Media Shuttle web servers. Instead, Media Shuttle utilizes a trust relationship to interact with identity gateways, like the Active Directory Federated Services gateway, to securely retrieve and validate access tokens for users.
For users managed exclusively in Media Shuttle, passwords are stored using secure “salted one-way hashes.” Passwords are not stored in clear text and what is stored can only be used to determine if a password provided by a user is correct. Passwords provided by users are tested by applying the “hashing process” and comparing the result to the stored value. The “salt” is random data that is included in the “hash” to prevent brute force dictionary attacks on the password database in the unlikely event of a breach. This is just one layer in the defense-in-depth strategy incorporated in the Media Shuttle design.
If you found this informative, check out part two in this series covering “the human factor and designing for the unpredictable.”