Is Security Enhanced or Hindered by Additional Software Layers on Top of Raw Storage?
Media professionals have many options for storing, organizing and accessing digital media assets. Options range from unadorned use of raw file systems to use of extensively, and often overly, featured media asset management systems that sit between users and storage. While there are many factors that influence the suitability of each approach for any given situation, security implications are a constant consideration. So is security enhanced or hindered by additional software layers on top of raw storage?
Multi-Layered Security
The “defense in depth” secure design principle advocates implementing multiple layers of protection around assets. The appropriate type and number of layers depends on the assets being protected and their associated value. The word “layer” is important because it conveys that an attacker must break through each “layer” in succession in order to successfully compromise an asset. In contrast, when there are multiple paths for accessing an asset, an attacker must only overcome the security mechanisms on one of the available paths to gain access to the asset – going through the open back door instead of the heavily fortified front door, so to speak.
So does accessing media through value-add software on top of storage, rather than interfacing with storage directly, represent an additional layer of security or does it leave an open back door exposed? Accessing media through application software almost always improves the security posture assuming underlying storage access controls are appropriately configured. Least privilege security principles advocate that only the people and systems that need access to a resource should have access to a resource, so it’s key that storage access controls are configured such that directly accessing the underlying assets isn’t an exploitable attack vector for an adversary.
Taking IT to a Higher Level
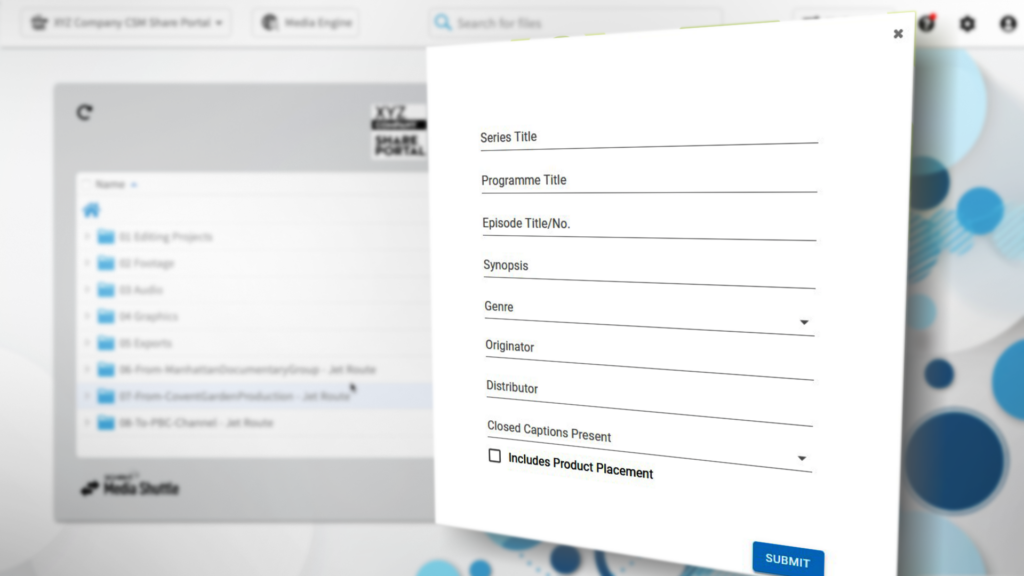
Because higher-level software often incorporates metadata that lower-level storage isn’t aware of, least privilege and appropriate classification of underlying assets can typically be managed more effectively. With well-designed software, this translates into a framework for controlling access that a non-technical administrator can more easily understand, eliminating the need to master obscure file or object storage access control mechanisms, and the potential for misconfiguration. Of course, file level access controls must be configured properly, but this can be managed as a somewhat independent concern by IT at system setup time and on a less frequent basis.
The higher-level awareness afforded by metadata also allows administrators to audit who accessed what using a model they are familiar with. It is extremely difficult to forensically determine why an asset was accessed from raw storage logs. Also, if the system enables operations on assets without removing them from the system — like viewing a proxy or partial download of an asset in the correct format — copies of assets outside of the system can be minimized. That said, care has to be taken to deliver the right set of features to users for the task at hand. Overly featured systems can become cumbersome and confusing to use, leading to mistakes or causing people to work around the system.
Media professionals have many options for storing, organizing and accessing digital media assets. Providing users a fit for purpose software layer on top of raw storage almost always delivers significant security benefits. Key to achieving security benefits is that underlying storage access controls are configured properly and that the features of the software being deployed are matched with the task at hand.